Security and Compliance
SOC 2 Type II certified. GDPR compliant. Enterprise access controls and a transparent AI safety commitment. Review our practices below or request full documentation.



Independently audited annually
EU data protection regulation
Enterprise customers
Compliance and Monitoring
SOC 2 Type II
Colossyan holds SOC 2 Type II certification, independently audited by a third-party firm. This covers security, availability, and confidentiality controls across our platform and infrastructure. Reports are available through our Trust Center under MNDA.
GDPR Compliance
Colossyan complies with the EU General Data Protection Regulation. We process personal data lawfully, maintain data processing agreements (DPAs), and support data subject access requests. Our privacy policy and DPA are available on request.

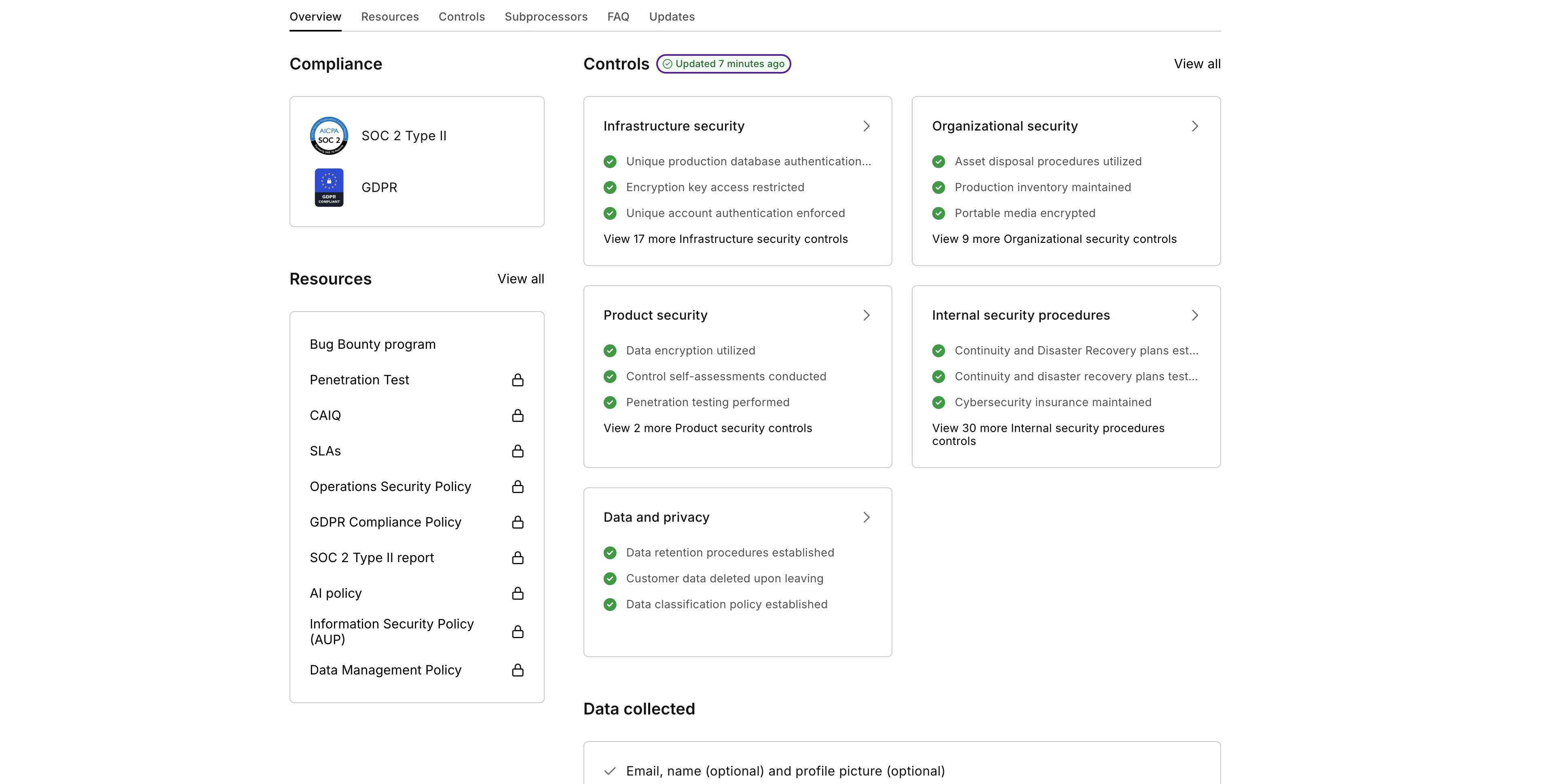
Trust Center
Our Trust Center at security.colossyan.com gives prospects and customers direct access to security documentation, policies, penetration test reports, and compliance certifications. We conduct annual third-party penetration tests. Reports are available under NDA.

Continuous Monitoring
Our attack surface is monitored in real time by UpGuard. Colossyan has maintained an UpGuard safety score above 900 for 12+ consecutive months. Current score and history are visible in our Trust Center.

We Do Not Train on Your Content
This is the most common question enterprise teams ask. Here is what it means in practice.
- • Your documents, scripts, and videos are never used to train our AI models
- • Our AI vendors are contractually prohibited from training on Colossyan input
- • All training data is lawfully sourced and properly licensed
- • Subprocessor list available through our Trust Center
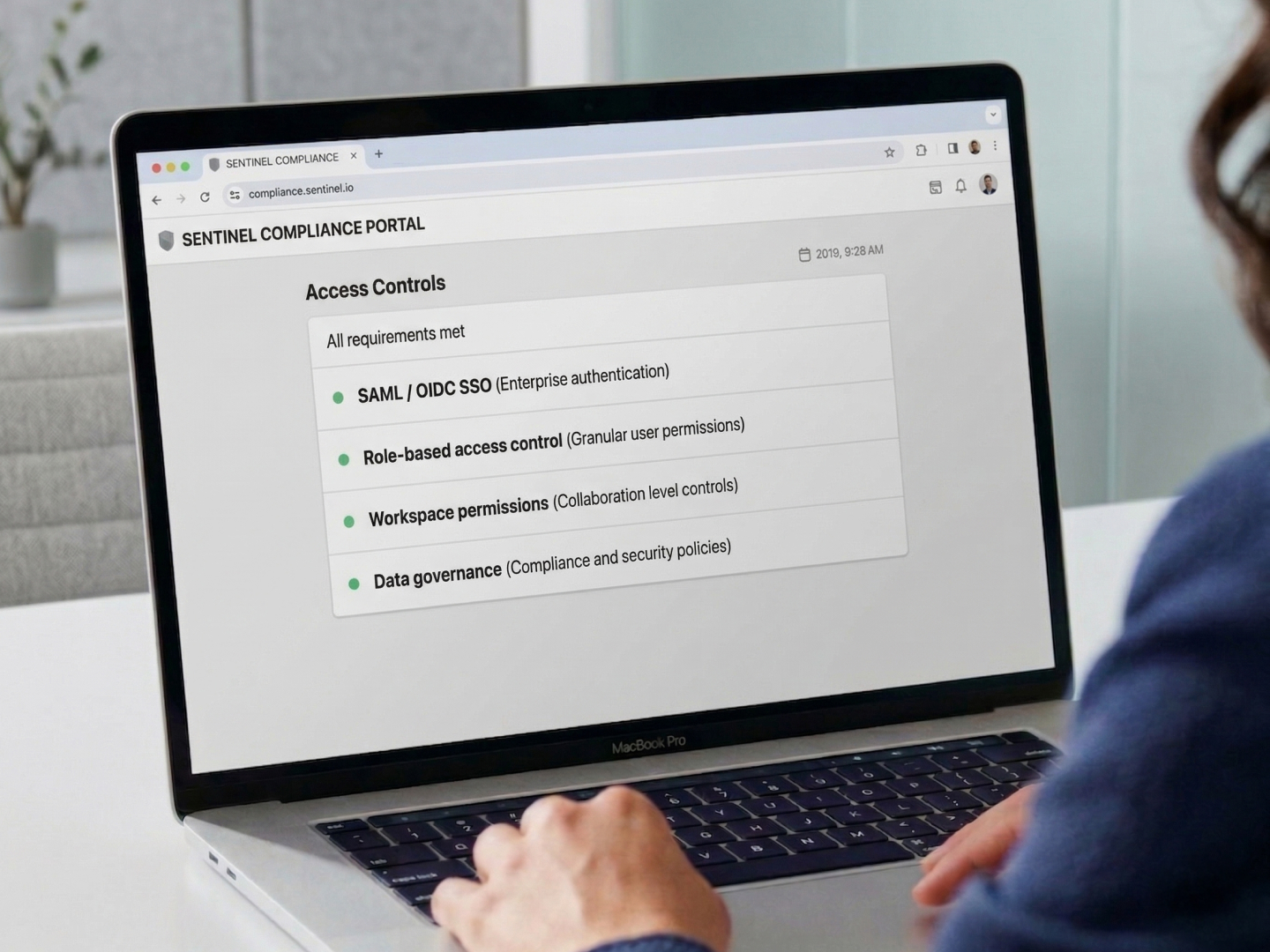
Built for Enterprise IT Requirements
Colossyan supports the access management, authentication, and governance controls enterprise IT teams require.
- • SAML and OIDC SSO integration for secure enterprise authentication
- • Custom roles and permissions at the workspace level
- • Multi-workspace architecture for privacy management and administrative oversight
- • MSAs and security questionnaire support for procurement teams
AI Safety Practices
We build AI to be secure and transparent. Our practices comply with the GDPR and follow the transparency and risk management principles of the EU AI Act.

How We Build and Train AI Models
- Training data is lawfully sourced and properly licensed
- Privacy and security by design from day one
- Humans stay involved in AI development and deployment
- Content filtering and moderation tools prevent harmful outputs
- All stock avatars created with full consent from real actors

Third-Party AI Partner Review
- Every AI integration undergoes a structured legal and security review before implementation
- We prioritize AI vendors with ISO 27001 or SOC 2 Type II certification and assess security posture before integration
- IP ownership, licensing rights, and DPAs must be aligned before we sign

How Our Team Uses AI
- High-impact decisions are made by people, not software
- No sensitive or proprietary information entered into AI tools without security and legal approval
- All AI tools go through our vendor management process with regular audits
How We Protect Your Data
From ingestion to storage to delivery, your training content is protected at every step.
Data in Transit
All data transmitted between your browser and Colossyan servers is encrypted using TLS 1.3. API communications use the same encryption standard.
Data at Rest
Customer data stored on our servers is encrypted at rest using AES-256. This includes uploaded documents, generated videos, course content, and user data.
Infrastructure
Colossyan runs on AWS infrastructure in EU and US regions. Our infrastructure is monitored continuously and reviewed as part of our SOC 2 Type II audit cycle.
Availability
99.9% uptime SLA commitment. Recovery Time Objective (RTO) and Recovery Point Objective (RPO) of 1 hour. Your training programs stay available when your teams need them.
Why Teams Choose Colossyan
“The biggest benefit of Colossyan is being able to have training material that never goes obsolete.” Read AmeriSave Mortgage case study

“We’ve been able to replace an average of 10 hours of walkthrough meetings every month by generating a Colossyan video.” Read Paramount Pictures case study

“Colossyan’s technology and its translation capabilities have revolutionized our training processes, especially in a multi-lingual environment like ours.” Read Sonesta case study

Security Questions
No. Colossyan does not use customer-uploaded documents, scripts, or generated training videos to train or fine-tune AI models. We also require this contractually from every AI vendor we integrate with. Your content remains your content.
Yes. Colossyan holds SOC 2 Type II certification, covering security, availability, and confidentiality. The certification is maintained through annual independent audits. SOC 2 reports are available through our Trust Center at security.colossyan.com under a mutual NDA.
Yes. Colossyan supports OIDC and SAML-based single sign-on for enterprise customers. This allows teams to authenticate through their existing identity provider (Okta, Azure AD, Google Workspace, etc.) without creating separate Colossyan credentials.
Colossyan infrastructure is hosted on AWS in EU and US regions. Specific data residency requirements can be discussed during the enterprise sales process. Contact your account manager for details.
Colossyan maintains an incident response plan covering detection, containment, notification, and remediation. In the event of a data breach, affected customers are notified within the timeframes required by GDPR (72 hours). Full incident response documentation is available through our Trust Center.
Visit our Trust Center at security.colossyan.com. You can request access to our full security documentation, including SOC 2 reports, penetration test results, and company policies. Some documents require a mutual NDA, which your Colossyan contact can arrange.
Yes. Colossyan supports MSAs (Master Service Agreements), custom DPAs, and can complete your organization's security questionnaire. Contact your account manager or reach out through the enterprise sales process.
You do. All documents, scripts, generated videos, and course content created in Colossyan belong to your organization. Colossyan does not claim any rights over customer-created content. Upon contract termination, you can export your content and request full deletion of your data.
Colossyan's AI practices follow the transparency and risk management principles of the EU AI Act. We maintain clear documentation of how our AI systems are built, how training data is sourced, and how outputs are monitored. Our full AI safety practices are detailed in the AI Safety section above.
Yes. Colossyan regularly completes vendor security questionnaires, AI risk assessments, and governance reviews for enterprise customers. We provide SOC 2 reports, penetration test results, DPAs, incident response documentation, and AI policy materials through our Trust Center. Contact your account manager to start the process.

Ready to Review Our Security Practices?
Visit our Trust Center for documentation, or book a demo to discuss your organization's specific security requirements.